How Cyber Security For Small Business Can Be Enhanced?
Since organizations of variable employee sizes may get the benefits from the effective conveniences when their businesses may be operated on the available digital platforms, all this is not possible if the cybersecurity challenges aren’t rendered well by them.
Moreover, the ones who are known as the QuickBooks Hosting Providers need to understand the fact that the cybersecurity field and the associated offerings have become a boon in today’s hyperconnected world where large, medium, and small-sized businesses are necessarily trying to connect with their potential customers.
Undoubtedly, smaller businesses may simply come into the claws of unpredictable and non-compensated cyber-attacks as they have typically been operating on fewer resources which are solely dedicated to cybersecurity and the related merits. Thus, these owners need to accept the strategies so that the cybersecurity for their assets may be enhanced and optimized at the required stages of development.
Some of the ways through which cybersecurity for smaller businesses is enhanced
Unavoidably, the prime motivation(s) for the individuals playing the role of cyber-criminals is nothing but financial gain.
If one visualizes the trajectories of the last few decades, this may be concluded that cyber-criminals have massively been growing in both – technical plus operational sophistication. Furthermore, such online assaulters can be a pervasive threat as they are now holding the personally-identifiable data or the information – or the payment details [at maximum times].
Besides, this sort of information has allowed cybercriminals to capture the profit margins from fraudulent activities since the available data may now be resold. Merely, when large businesses acquiring more than a ninety-people’s workforce have more data to get stolen, the small-sized businesses may become attractive targets – for the cybercriminals [that are less sophisticated].
# Way Number One – Lack-of-time, knowledge plus the budget
If one analyzes the importance of managing the time-frames with the available knowledge bases and the budgets too, this may be estimated that all three reasons will explain to you [including the experts of Cloud QuickBooks hosting] why the small-scale businesses fail to capture sufficient cybersecurity till the date [today].
Even the implementation of the relevant tools – that may offer protection to the existing applications and the hardware resources driving them – will surely come forward with a not-affordable price tag[s] thereby making the same harder for these small businesses to capture the implementation of the relevant tools and the terminologies somewhere revolving around cybersecurity.
However, the developers or the business owners may adopt three-to-four cost-effective and simple practices that may keep data and related devices secure – without allowing the cybercriminals to steal the wealth stored in the bank accounts.
# Way Number Two – Educating the employees
Employees are assertively the weakest links for cyberattacks – in a company’s fight against evolving cybersecurity challenges.
Furthermore, the ones well-versed with the Qb Cloud and the relevant add-ons must accept the fact that training the existing employees about the cybersecurity basics and the advanced-level aspects – at regular or frequent times – is the simpler but the most effective way(s) to protect the existing businesses from those cyberattacks.

Even the existing companies may acquire the same via e-learning, conducting related seminars regularly – for employees – so that they can identify the potential threats and respond well – with much attentiveness, and at last – a-few-on-boarding-talks.
All such preventative measures will help the existing employees to avoid becoming the victims of that phishing or other cybersecurity scams.
# Way Number Three – MFI [Multi-factor-identification]
MFI – primarily known as Multi-factor-identification can be implemented onto multiple channels. Also, this may be like a win-win situation as this will quickly offer protection to the datasets – stored either at the servers somewhere accessing the personal plus the professional devices.
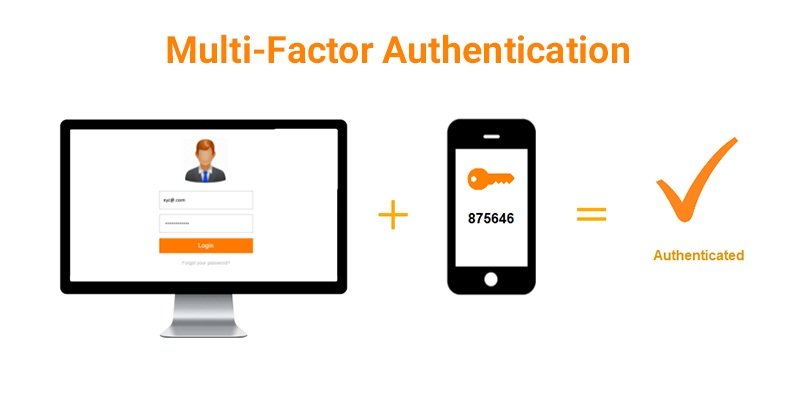
Indistinguishably, at times a cybercriminal becomes successful in obtaining the person’s credentials – either the password or the username, the situation will be more difficult – for the criminal – since the MFI – Multi-factor-identification won’t allow the cybercriminal to misuse such information(s).
Henceforth, the use of MFI – Multi-factor-identification [or this may also be called the authentication] has strengthened the pillars of the existing network as the cybercriminals may not target the person with much comfortability and feasibility. So, the criminals may now move on to the other targets – since the MFi is now protecting the person’s identification.
# Way Number Four – Implementing the strong-password-policies
While creating and simultaneously – enforcing strong password policies – small-scale businesses may now improvise the existing pillars of cybersecurity. But, this becomes necessary to investigate if or not the existing employees are nodding their heads for changing the passwords – after the ninety-day(s) period.
Additionally, all such passwords must be created in a manner that may sound complex – to the hackers – and even no single password should be allowed to use for more than [one] log-in. Though the same is tedious, this may be an effective plus precautionary measure as the powerhouse against the existing or the futuristic cyberattacks has now been established thereby reducing the risks – with utmost diligence and economical perspectives.
# Way Number Five – Installing the updated AV [Antivirus] Software(s)
In most obvious times, phishing attacks may commonly be used against small-level businesses and also, business travelers too.
Even such sorts of attacks occur when the cybercriminals refer to the citations of the text messages and also, the emails – for impersonating the ones primarily involved in creating the malicious links [or the attachments] that can be used for installing the malware.
Therefore, acquiring the updated AV [Antivirus] software(s) across all the working devices of the companies and the networks supporting them is a way for preventing malware and other types of viruses from attacking the existing networks of these small-scale companies.
# Way Number Six – Creating the backups at regular intervals
This is necessary to create a backup of the files supporting your businesses. Either you may regularly restore the data before the potential breaches destroy the business modules or allow the hackers to steal the important datasets driving the operations resourcefully in crucial moments.
To ensure that the latest backup is accessed whenever needed, this becomes mandatory to check the backup on a regular basis – this ensures that the backup(s) is functioning aptly. Also, it is important to remember that employees traveling for the business-purposes may fall into the trap of cybersecurity risk.
If we dig deeper into the most recent Travel Risk [International SOS’ ]Outlook study, this can be revealed that less than one-third of the existing small-scale organizations have included cybersecurity in their mitigation [and the travel-risk-management] policies.
Because cybersecurity threats can’t be restricted to QuickBooks Cloud users, and geological divisions, thus the employees must access the company’s information either on mobile devices or laptops – at that instance. This is because if such smartphones or tablets are used simultaneously – while the employees are traveling for business – the chances of facing the cyberattacks’ risks increase somehow.
Should the listed-above ways be ignored or accepted with sincerity?
The potential attackers may control the infrastructure on which communications regarding the company’s targets and their portable devices take place – either regularly or eventually. Therefore, this becomes mandatory for business travelers to avoid connecting with unsecured Wi-Fi networks.
Unluckily, if they do so, the chances for cyberattacks may increase and this is possible that the travelers may lose their sensitive data – even after taking cost-effective plus precautionary measures at that instance somewhere helping them reduce the cyberattacks’ risks.
What they may do is implement the listed-above simple measures through which the risk of attacks may be reduced extensively.
Otherwise, the attacks become more vulnerable and they [means the business travelers or the employees] may get fascinated towards becoming a cybercriminal – who may not follow the above ways and offer the uncontrollable destruction to the available processes and the infrastructures of the small-scale businesses.





